Manage Your IoT Data Streams with Custom Permissions for MQTT Clients on HiveMQ Cloud
In one of our articles, Enhanced Security with MQTT Client Credentials Feature on HiveMQ Cloud, we highlighted how the HiveMQ Cloud’s MQTT client credentials can help you achieve security for your IoT projects.
HiveMQ Cloud is excited to release custom permissions, for its Free and PAYG tiers, to help you secure your IoT projects. In this blog , we’ll discuss these custom permissions, why you need them, and how to use them with HiveMQ Cloud.
Introducing Custom Permissions
MQTT credentials are essential for securing your client connections. In March 2023, we introduced three predefined permissions, Publish only, Subscribe only, and Publish and subscribe for MQTT credentials within the Free and PAYG versions of the HiveMQ Cloud.
With the latest release, we have also added custom permissions for MQTT clients. With these custom permissions, you have additional control over your data streams.
Let’s look at this new feature in detail.
Feature Details
In addition to the MQTT Client permissions, you can now create custom permissions for your data streams. This feature is available under Access Management.
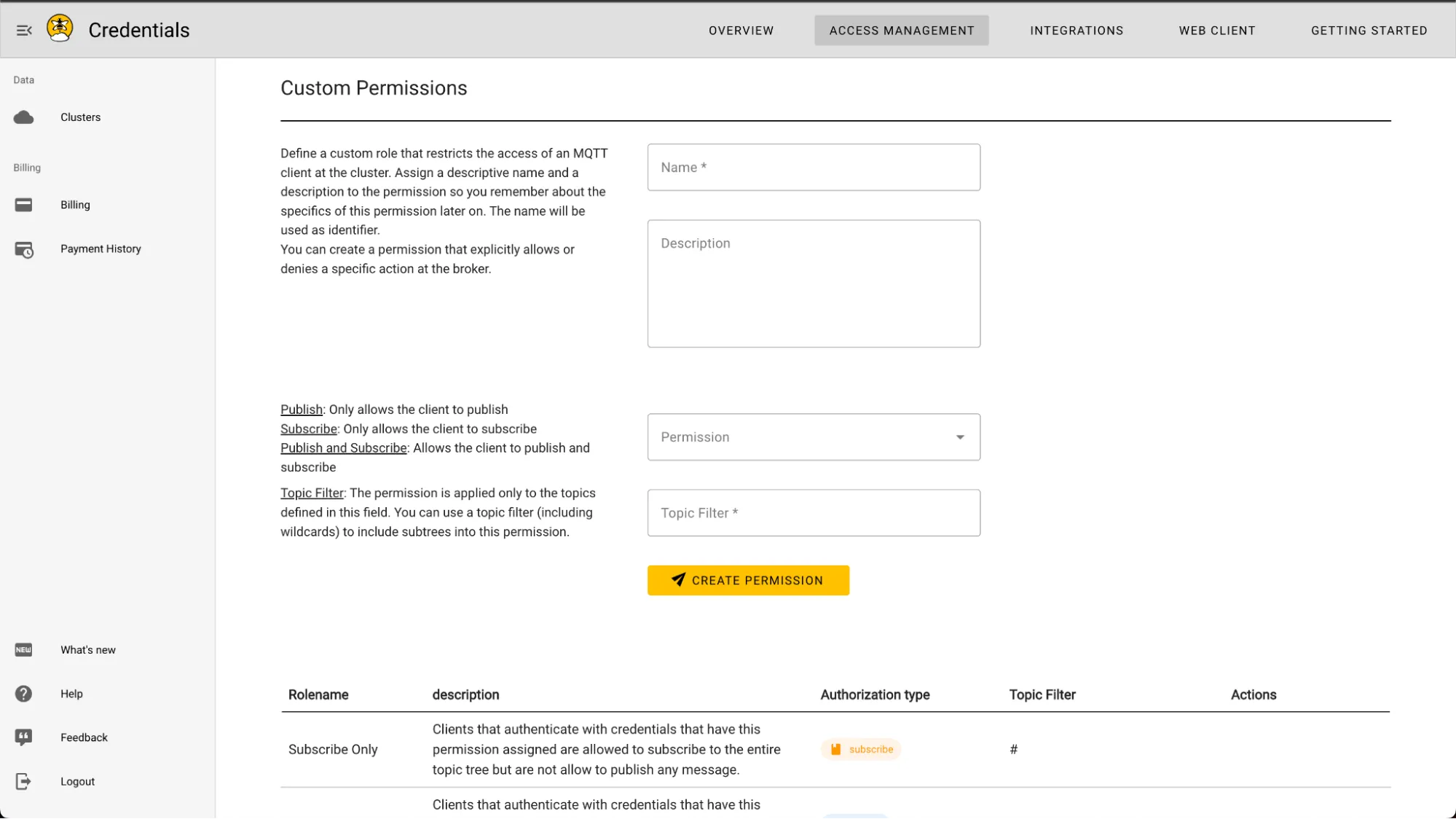 HiveMQ Cloud Custom Permissions User Interface
HiveMQ Cloud Custom Permissions User Interface
With this feature, you can create custom permission with a name of your choice. You can also add a description.
The custom permission has four elements:
Name: you can create custom permission with a name of your choice.
Description: you can optionally add a description to define the use of the permission.
Permission type: You can specify the custom permission to have one of the following attributes:
Publish only
Subscribe only, or
Publish and subscribe.
Filter: you can filter the topic you want to associate with this role. This filter also works with MQTT wildcards.
With the Free and PAYG versions of HiveMQ Cloud, you can currently use one topic filter per permission.
Why Do You Need a Custom Permission?
In addition to restricting the publish/subscribe access for MQTT clients, you may also want to limit your MQTT clients’ access to specific topics. With this, you can easily differentiate the different MQTT clients for your IoT project and ensure the data streams from clients remain separate.
Another example where you can use custom permissions is when you have different devices assigned to the customers working in multi-tenant broker instances and you need to manage the datastreams from these different devices.
Because custom permissions can reduce the scope of the client to specific topics, it helps minimize the impact of security breaches.
A Use Case for Client Permissions
Here is an example of a simple use case where client permissions are helpful. Imagine we collect simple atmospheric data for its analysis and distribution.
There are three sensors:
Sensor A can only publish to the topic weather/temperature. The custom permission is defined as “publish temperature”.
Sensor B can only publish to the topic weather/humidity. The custom permission is defined as “publish humidity”.
Sensor C can only publish to the topic weather/pressure. The custom permission is defined as “publish pressure”.
Two additional services are using all this data:
Database for storing the data and using the data at a later stage.
Workstation that can use the data to compute weather forecasting.
These services do not need custom permissions, as the database and workstation must publish and subscribe to all topics. Therefore we can use the predefined role “publish and subscribe”. However, one can explicitly control the data flow by assigning “publish and subscribe” permissions when defining the MQTT client credentials.
If a display and a dashboard are also connected to the broker, then:
Display X subscribes to the topic weather/temperature and displays the temperature in real-time. The custom permission is defined as “subscribe temperature”.
Dashboard Y subscribes to the topic weather/forecast and displays the forecasted data. The custom permission is defined as “subscribe forecast”.
Thus, these different custom permissions help you have complete control over your IoT data streams.
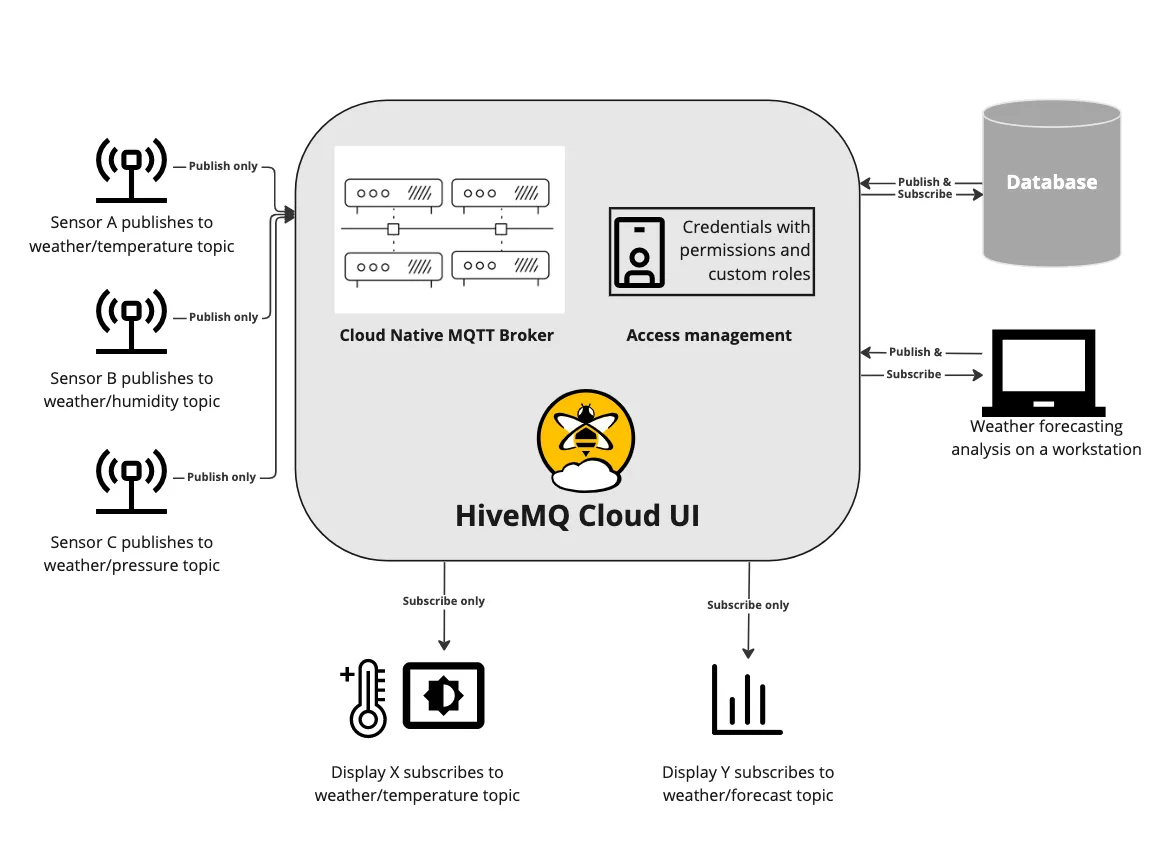 Graphical Representation of the Use-Case
Graphical Representation of the Use-Case
In the Free and PAYG versions of the HiveMQ Cloud, such credentials can look as follows:
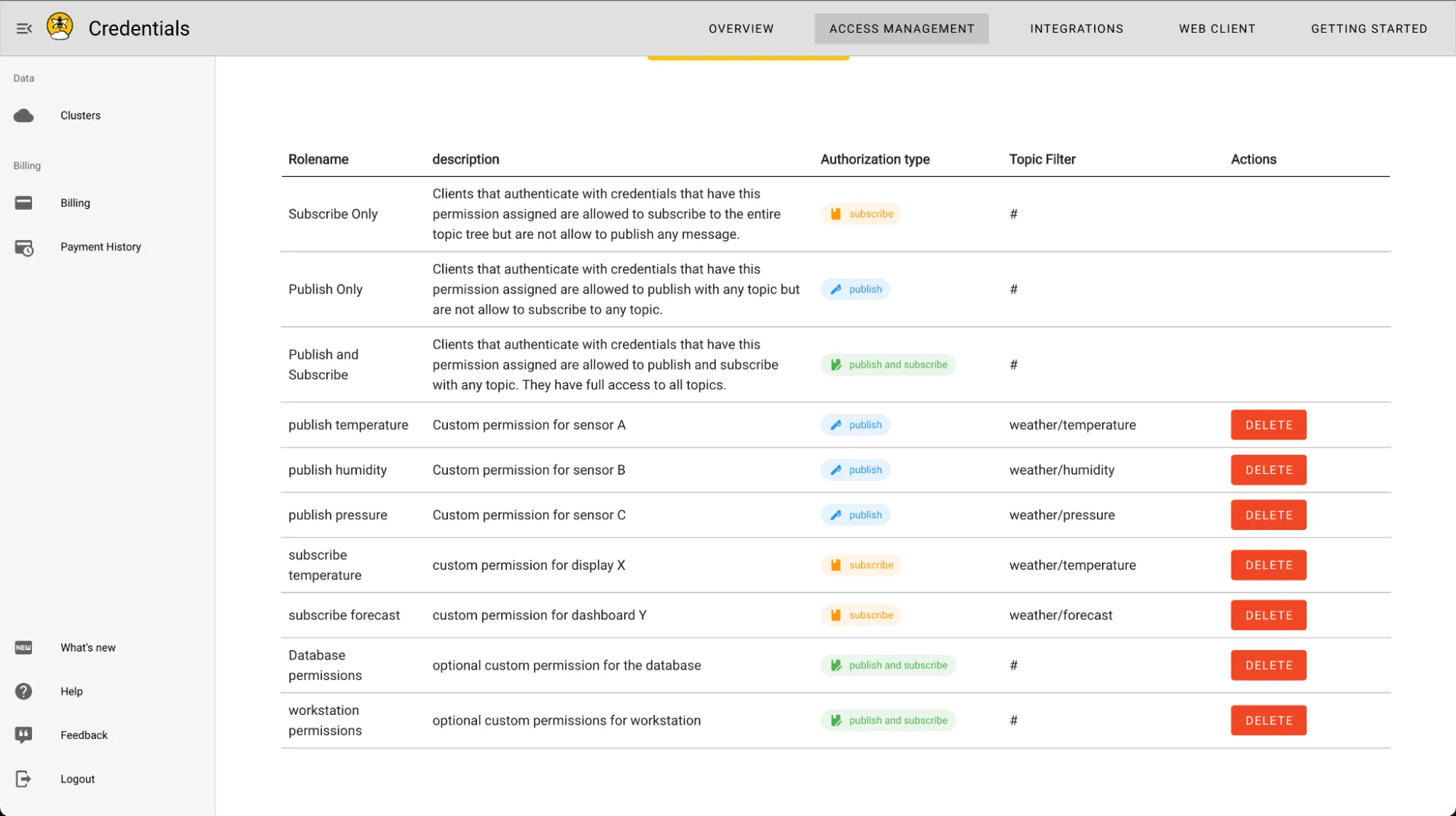 Custom Permissions for the Described Use-case as Seen in the HiveMQ Cloud UI
Custom Permissions for the Described Use-case as Seen in the HiveMQ Cloud UI
Get Started
MQTT custom permissions allow you to control your IoT projects’ different data streams, strengthening the security. You can also control what connected clients can and cannot do, once they are connected. In addition, separating customer data streams with custom permissions allows you to use your HiveMQ Cloud cluster as a multi-tenant broker. With HiveMQ Cloud’s easy-to-use portal UI, managing your MQTT datastreams with custom permissions is simplified in the Free and PAYG tiers.
Now that you know about the magic of the custom permissions, are you ready to try them out?
Get started with a complete MQTT platform for testing and small-scale IoT projects. Enjoy a 15-day free trial with exclusive features like unlimited connections, up to 1MB/s data throughput, 99.95% uptime, 24/7 support, client certificate authentication, and more.

Shashank Sharma
Shashank Sharma is a Sr. Product Marketing Manager at HiveMQ. He is passionate about technology, supporting customers, and enabling developer-centric workflows. He focuses on the HiveMQ Cloud offerings and has previous experience in application software tooling, autonomous driving, and numerical computing.
